When people think of SIM swapping, they may imagine a Mission Impossible scenario where a thief swaps out the physical SIM card on your phone. But the fact is that SIM swapping is much easier than that for data thieves — and they never need to make contact with you at all. Get the facts on SIM swapping (also called simjacking, SIM hijacking and SIM fraud) to protect yourself and your company.
How Your SIM Could Provide Access To Your Accounts
SIM stands for Subscriber Identity Module. It’s a small card that slips into your smartphone that identifies you to your mobile carrier. Without a SIM card, phones can’t make calls or send text messages. There are two basic types of SIM cards used by most carriers, but for the purpose of security they are the same.
The SIM is what makes it possible for you to buy a new phone, pop in the SIM card, and it automatically has your number. But a data thief doesn’t need to come near you, or your phone, to swap or hijack your SIM.
Here’s how it works. The data thief gathers information on you, usually from social media, and uses it to impersonate you with your cell phone carrier. They get the carrier to transfer your SIM to another device. They then attempt to login to your other accounts (e.g., bank accounts) and because they have your SIM, any messages, warnings or Multi-Factor Authentication (MFA) by text goes to them.
After the SIM swap, your phone can no longer make calls or texts. Your apps will probably still work if you have access to WiFi.
How Common is SIM Swapping?
SIM hijacking is not as common as phishing and email scams, but it is on the rise. In August 2019, Twitter founder Jack Dorsey was a victim of SIM swapping. In this case, fraudsters used his SIM to gain access to his Twitter account and posted offensive messages for 15 minutes. A March story on CNN.com told the story of Robert Ross, who lost his life savings when his SIM was hijacked in 2018.
We should note that the most recent Twitter hack that tweeted a cryptocurrency scam from the accounts of Bill Gates, Elon Musk, Apple and others was NOT a SIM swap attack. Instead hackers gained access to credentials by targeting a small number of Twitter staff to perform certain actions that provided them access. This is another tactic called social engineering.
SIM swapping is a growing threat, with hacking rings found across Europe and South America. Attacks in the U.S. are becoming more common.
Signs That Your SIM May Have Been Swapped
If your SIM has been swapped to another device, it will stop working on yours immediately. So, if you suddenly find yourself unable to place calls or texts, SIM swapping is a possibility. Other signs include:
- Posts appearing on your social media accounts that are not yours.
- Notification that your SIM is being used on another device from your carrier.
- You’re unable to access your accounts, like bank accounts and credit cards.
If you think you have been a victim of SIM swapping, notify your bank, phone carrier and other organizations immediately. If your company is a Convergence Networks customer, call us ASAP so our data security experts can work to prevent hacks to your business accounts using the swapped SIM. If you think the scammer might have your social, credit card or other information, go to IdentityTheft.gov and take the steps provided.
Protect Yourself From SIM Swapping
Protect yourself from SIM swapping with these steps:
- Enable Multi-Factor Authentication (MFA) on all your accounts. When you login to your accounts from a new device or for the first time in a while, your account will require a code to authenticate you.
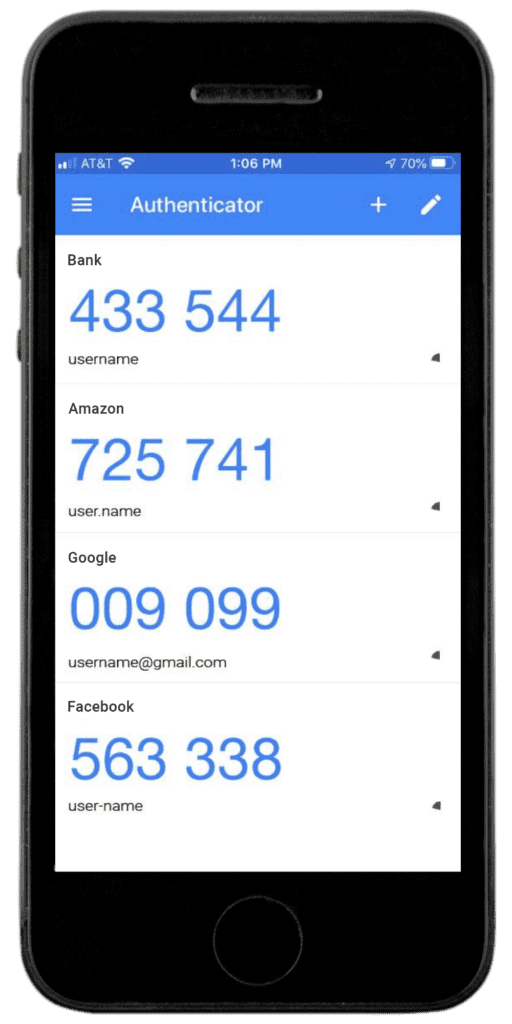
- Use an app (not SMS messages) to get authentication codes, such as Microsoft Authenticator (App Store / Play) or Google Authenticator (App Store / Play). The apps can be linked to multiple accounts and generate new codes every 30 seconds or so. So whenever you are prompted to enter a code to login, a fresh code is available in the app for that platform.
- Make sure your cell phone account is using a unique, strong password (ideally with upper and lowercase letters, numbers and a special character). DO NOT include any personal information in your passwords like your name or date of birth. These tips should also be used for all your passwords.
- Request that your carrier use a separate PIN code or passcode to make account changes. It is becoming more common for carriers to offer this option.
- Never give personal information to people who call, email or text you out of the blue. These can be phishing attempts to gain the data needed to breach your accounts (or convince your phone carrier they are you and swap your SIM). When in doubt, call the agency directly or go to their website (do not click the email links, they may take you to a site meant to look legit, but that is part of the scam).
- Avoid posting personal information on public sites, especially your full name, address and phone number.
The best protection against SIM swapping and other cyber crime for your business is a comprehensive cyber security plan. Contact us to request a free assessment or discuss your cyber security needs.














