Wednesday, May 6, 2026
1 p.m. ET / 10 a.m. PT
We are pleased to share that Certinet Systems is now part of Convergence Networks. Learn More.
We provide businesses like yours with IT support, proactive monitoring, and preventive maintenance.
Co-managed IT is a collaboration that works well for companies that want to keep in-house IT staff while also increasing IT capacity and specialized expertise.
We will design a customized IT helpdesk solution that meets your current business needs and scales with you as you grow.
We provide scalable, secure, and cost-effective network support that evolves with your growing business.
Providing organizations with comprehensive backup and disaster recovery solutions whether on premise or in the cloud.
Benefits from expert guidance, strategic planning and a proactive approach to IT management that drives success.
We provide cybersecurity solutions and support designed to protect your networks, assets and data while ensuring compliance with your industry regulations
We provide Zero Trust Security and Application Safeguarding to protect your environment from internal and external threats.
We provide services to assess your risk, strengthen your cybersecurity program and orient your team with solid procedures and training.
We provide the next generation of managed security services with a focus on real-time threat detection, threat hunting and active response.
We ensure your business becomes and stays compliant with all relevant regulations, safeguarding your organization’s sensitive data and reputation.
We provide ongoing services and one-time engagements to improved your cybersecurity and safeguard your critical data and assets.
Pen testing simulates a real-world cyberattack to uncover potential weaknesses before malicious actors can exploit them.
We take a holistic approach to ensuring your organization achieves and maintains compliance with Cybersecurity Maturity Model Certification (CMMC) standards.
We’ll craft customized, secure cloud solutions that meet your organization’s needs. From strategic planning to execution, our cloud migration services are designed to help your business attain smooth transitions.
We create and maintain secure, scalable and high-performing cloud environments that can be used to set yourself apart from the competition.
As a Microsoft Partner, Convergence Networks has access to exclusive training, products and tools to support our clients. We also offer tools and resources that are only available to Microsoft Partners.
We specialize in guiding businesses through cloud migrations and with leveraging Microsoft 365 benefits without technical obstacles.
We explore the specific advantages and potential challenges of adopting Microsoft Azure for your organization, help you understand how Azure fits into your overall business strategy and how it can be tailored to meet your distinct objectives.
Our team will partner with you to consolidate all your voice service needs into one place using a Microsoft Teams Phone system.
We provide the next generation of managed security services with a focus on real-time threat detection, threat hunting and active response.
Leverage the power of Microsoft 365 for modern and secure collaboration. Convergence Networks helps you unlock its full value through expert implementation, change management and tailored training programs that achieve results.
Modernize legacy applications for a faster, safer, more agile business. Our application modernization services are designed to reduce risk, accelerate business outcomes and create tools your team will want to use.
Stop wasting time on manual work. Let automation do the heavy lifting. We help you transition from manual to modern with secure, high-impact Business Process Automation (BPA) services.
Connect business-critical apps to improve security, visibility and operational control with cloud integration services. Our integration services turn disconnected apps into a secure, manageable, and unified system.
Improve connection, support employee growth and foster an inclusive culture with secure Microsoft employee engagement solutions. We help organizations support employees throughout their entire journey.
Unlock business success with our Data Analytics Services. Visualize trends and make smarter data-driven decisions. Identify trends, explore relationships in your data, and share information with your team with ease.
Transform how your team works with a secure, customized SharePoint solution built for Microsoft 365 and your business needs. Unlock the full potential of your business and 365 investment with expert SharePoint services.
We provide the next generation of managed security services with a focus on real-time threat detection, threat hunting and active response.
Our Copilot Factory delivers AI Copilots tailored to the unique needs of organizations. Discover new productivity and greater achievement.
Leverage secure AI adoption with expert-led deployment, training, policy guidance, and data protection. We help organizations adopt tools like Microsoft Copilot and other generative AI with strong data security protocols built-in.
You need an expert in your field. With over 20 years of experience in all areas of technology, we have your
We pulled together the most common business IT questions and provided some answers.
We are a security first IT services firm providing
We approach our clients with a focus on their business goals and requirements before recommending solutions to help achieve the desired outcomes. Learn more about what makes us unique.
Our core mission as a company is to help and empower people. We want to lend our time and resources to these organizations as way to give back and support all they do for our communities.
If your company does business with government contractors, you’ve likely heard of the Cybersecurity Maturity Model Certification (CMMC). If you’re new to CMMC, here’s what it means in a nutshell. CMMC is the mandated requirements set by the government and the Department of Defense for manufacturers and companies in the Defense Industrial Base. The goal is to ensure adequate cybersecurity protections are in place for the contract information shared by the government.
If it sounds like a mouthful, you’re right! But in the end, it is important to continue to do business with them. The government wants to make sure the supply chain companies it works with are protecting their information. CMMC is essentially designed to make sure manufacturers and companies uphold and certify to a certain level of cybersecurity maturity and hygiene.
The manufacturing industry was one of the first to be hit hard with the new standards, but it will in fact be trickling down to other industries.
Prior to CMMC, defense contractors were expected to meet the DFARS assessment and NIST 800-171, which continues to be an exceptional benchmark for cybersecurity measures. While NIST 800-171 was great, there lacked a certain level of accountability. So, companies were able to operate on a “pinky-swear” model. A self-attestation model. Companies could basically fill out a questionnaire and while you were required to document all the compliance and agree to meeting all 110 security controls, there was no scrutiny attached to it and hackers exploit this over and over again.
Which is why CMMC was introduced.
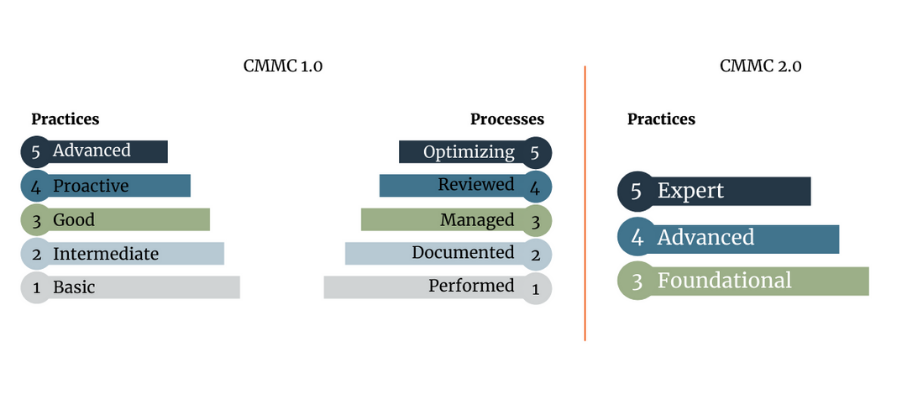
There’s a 2.0? What about 1.0? CMMC 2.0 is a shift in requirements from the original CMMC standard. The government realized meeting CMMC for many small businesses was going to be burdensome. CMMC 2.0 is a simplification and reduction of the overhead required for smaller organizations. So, take a deep breath. Before you stress out trying to understand and meet CMMC, let’s look at what CMMC 2.0 means and what it means for you.
While the DOD still appears to be making the determination and nothing is finalized or set in stone yet, previous statements suggest that you can self-attest but will need a high-level executive within your organization to provide a statement of acknowledgement that you meet the requirements. This final piece is the accountability that was missing with NIST 800-171.
With CMMC 1.0, there were five different levels a company could meet. With CMMC 2.0 there are three.
If you supply the DoD directly, or subcontract with someone who does, CMMC applies to you. Here’s how you can prepare your business:
Even though CMMC has to do with the security of your information, it is crucial to understand that CMMC is not just an IT issue. CMMC impacts everyone within the organization. As a business leader, it is important for you to understand that this a journey. It cannot be achieved by simply purchasing a piece of software. It is not a quick one-and-done kind of a thing. Because of this, it will be less of a headache for you, and you will thank yourself later if you start by integrating security into the way you do business.
Check out the podcast for more insight into CMMC 2.0 and what it means for your business! If this is something you need help navigating contact us. We can help you map your journey.
To connect, please enter the 6-digit code given to you by your Network Administrator: