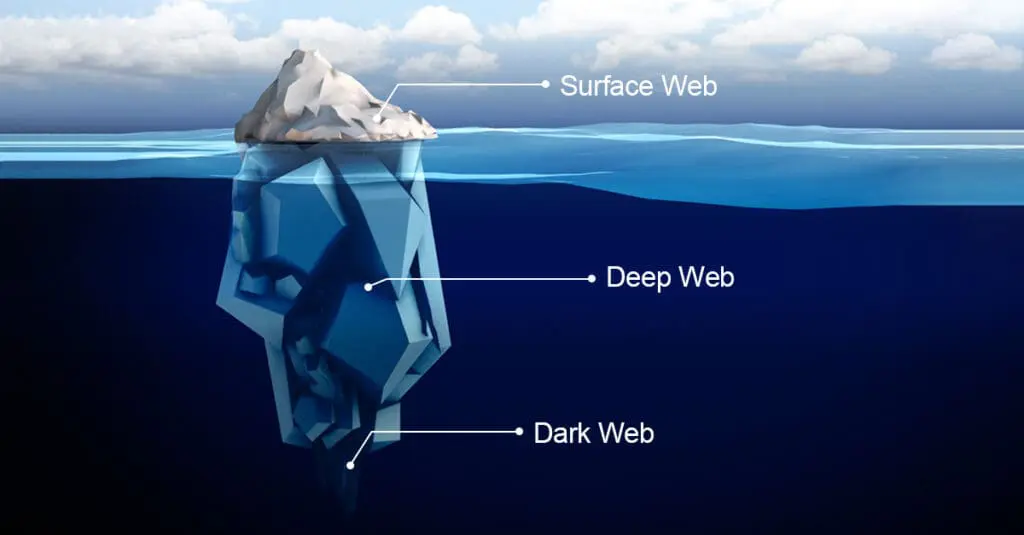
When most people think of the internet, they picture websites like Google, Amazon, LinkedIn, or YouTube. But understanding the dark web is just as important for business security. The part of the internet we see daily is called the surface web. It’s the part that search engines can find and display. Beneath the surface lies a much larger, hidden portion known as the deep web, and buried even further within is the dark web.
What is the Dark Web?
The dark web is a small, hidden part of the internet that isn’t indexed by search engines. You can’t get there by accident. To access it, you need special tools like the Tor browser (short for The Onion Router). Once you’re in, you visit websites with addresses ending in .onion instead of .com or .org. These sites can’t be viewed using standard browsers like Chrome or Safari.
Unlike the open internet, which is accessible to everyone, the dark web is built around privacy and anonymity. It routes your connection through several servers, each peeling back a layer of encryption, much like peeling an onion. This method, called onion routing, helps conceal both the user and the host’s identities.
Some people use the dark web for legitimate reasons, journalists protecting sources, or individuals living in regions with censorship. But it’s also known for illegal activity. In fact, as of 2020, nearly 57% of content on the dark web was considered illegal
Decoding the Web’s Layers: Surface, Deep, and Dark
Here’s a simple breakdown:
- Surface Web: Public sites you find through Google and other search engines. It’s only about 4–10% of the internet.
- Deep Web: Includes all private or restricted-access content like your email inbox, cloud storage, online banking, or internal business portals. It makes up around 90–96% of the internet.
- Dark Web: A small part of the deep web. It requires tools like Tor and uses .onion addresses. It’s where much of the illegal activity takes place.
Even though it makes up less than 1% of the internet, the dark web is constantly evolving and remains a major concern for businesses.
Why You Should Be Aware

Understanding the dark web is important. You may never visit the dark web, but that doesn’t mean it can’t affect your business. Here’s how:
Stolen Data Marketplaces
The dark web is a known destination for trading stolen data. This includes customer records, login credentials, payment card information, and confidential business data. Once this data is sold, it can be used to target your systems or impersonate your employees.
Credential Stuffing and Account Takeovers
Cybercriminals often buy stolen usernames and passwords, then use automated tools to try those credentials on other platforms. If your employees reuse passwords, attackers could gain access to internal systems.
Sale of Malware and Exploits
Hacking tools, phishing kits, ransomware, and other forms of malicious software are readily available on the dark web. These tools can be used by attackers with little technical knowledge to carry out damaging cyberattacks.
Insider Threats
In some cases, disgruntled employees may turn to the dark web to leak sensitive information or work with cybercriminals. Understanding this risk can help you monitor for unusual behaviour and implement appropriate safeguards.
Reputational and Financial Risk
If your company data shows up on the dark web, whether it’s internal documents, client lists, or security credentials, it can lead to serious reputational damage. Customers may lose trust. Regulators may get involved. The financial impact can be substantial. Read about the true cost of a data breach in our recent blog “The Cost of a Data Breach: Why Investing in Cybersecurity Saves Money.”
What Can You Do?

You don’t need to become a dark web expert to protect your business. But taking a few practical steps goes a long way.
Build a Strong Cybersecurity Foundation
Use strong password policies, multi-factor authentication, and keep software updated. Train your staff regularly to recognize phishing and suspicious behaviour. The goal is to reduce the chances of data being stolen in the first place.
Invest in Dark Web Monitoring
There are tools that monitor the dark web for mentions of your company’s credentials, domains, and sensitive information. These tools alert you early if something is exposed, giving you a chance to take action before serious damage is done.
Perform Regular Risk Assessments
Understanding your current vulnerabilities helps you close security gaps before someone else finds them. This includes reviewing employee access, patching systems, and testing incident response plans.
Work With a Security-Focused IT Partner
You don’t have to manage all this on your own. A trusted IT partner can help you implement and manage security strategies that reduce risk and improve resilience.
The dark web is not a distant or abstract threat. It’s real, and it’s growing. Understanding the dark web and how it works is the first step to protecting your business. The next step is taking action.
Reach out to us today. Convergence Networks is here to help you stay ahead of the risks, protect what matters, and build a more secure future for your team and your customers.














