Wednesday, May 6, 2026
1 p.m. ET / 10 a.m. PT
We are pleased to share that Certinet Systems is now part of Convergence Networks. Learn More.
We provide businesses like yours with IT support, proactive monitoring, and preventive maintenance.
Co-managed IT is a collaboration that works well for companies that want to keep in-house IT staff while also increasing IT capacity and specialized expertise.
We will design a customized IT helpdesk solution that meets your current business needs and scales with you as you grow.
We provide scalable, secure, and cost-effective network support that evolves with your growing business.
Providing organizations with comprehensive backup and disaster recovery solutions whether on premise or in the cloud.
Benefits from expert guidance, strategic planning and a proactive approach to IT management that drives success.
We provide cybersecurity solutions and support designed to protect your networks, assets and data while ensuring compliance with your industry regulations
We provide Zero Trust Security and Application Safeguarding to protect your environment from internal and external threats.
We provide services to assess your risk, strengthen your cybersecurity program and orient your team with solid procedures and training.
We provide the next generation of managed security services with a focus on real-time threat detection, threat hunting and active response.
We ensure your business becomes and stays compliant with all relevant regulations, safeguarding your organization’s sensitive data and reputation.
We provide ongoing services and one-time engagements to improved your cybersecurity and safeguard your critical data and assets.
Pen testing simulates a real-world cyberattack to uncover potential weaknesses before malicious actors can exploit them.
We take a holistic approach to ensuring your organization achieves and maintains compliance with Cybersecurity Maturity Model Certification (CMMC) standards.
We’ll craft customized, secure cloud solutions that meet your organization’s needs. From strategic planning to execution, our cloud migration services are designed to help your business attain smooth transitions.
We create and maintain secure, scalable and high-performing cloud environments that can be used to set yourself apart from the competition.
As a Microsoft Partner, Convergence Networks has access to exclusive training, products and tools to support our clients. We also offer tools and resources that are only available to Microsoft Partners.
We specialize in guiding businesses through cloud migrations and with leveraging Microsoft 365 benefits without technical obstacles.
We explore the specific advantages and potential challenges of adopting Microsoft Azure for your organization, help you understand how Azure fits into your overall business strategy and how it can be tailored to meet your distinct objectives.
Our team will partner with you to consolidate all your voice service needs into one place using a Microsoft Teams Phone system.
We provide the next generation of managed security services with a focus on real-time threat detection, threat hunting and active response.
Leverage the power of Microsoft 365 for modern and secure collaboration. Convergence Networks helps you unlock its full value through expert implementation, change management and tailored training programs that achieve results.
Modernize legacy applications for a faster, safer, more agile business. Our application modernization services are designed to reduce risk, accelerate business outcomes and create tools your team will want to use.
Stop wasting time on manual work. Let automation do the heavy lifting. We help you transition from manual to modern with secure, high-impact Business Process Automation (BPA) services.
Connect business-critical apps to improve security, visibility and operational control with cloud integration services. Our integration services turn disconnected apps into a secure, manageable, and unified system.
Improve connection, support employee growth and foster an inclusive culture with secure Microsoft employee engagement solutions. We help organizations support employees throughout their entire journey.
Unlock business success with our Data Analytics Services. Visualize trends and make smarter data-driven decisions. Identify trends, explore relationships in your data, and share information with your team with ease.
Transform how your team works with a secure, customized SharePoint solution built for Microsoft 365 and your business needs. Unlock the full potential of your business and 365 investment with expert SharePoint services.
We provide the next generation of managed security services with a focus on real-time threat detection, threat hunting and active response.
Our Copilot Factory delivers AI Copilots tailored to the unique needs of organizations. Discover new productivity and greater achievement.
Leverage secure AI adoption with expert-led deployment, training, policy guidance, and data protection. We help organizations adopt tools like Microsoft Copilot and other generative AI with strong data security protocols built-in.
You need an expert in your field. With over 20 years of experience in all areas of technology, we have your
We pulled together the most common business IT questions and provided some answers.
We are a security first IT services firm providing
We approach our clients with a focus on their business goals and requirements before recommending solutions to help achieve the desired outcomes. Learn more about what makes us unique.
Our core mission as a company is to help and empower people. We want to lend our time and resources to these organizations as a way to give back and support all they do for our communities.
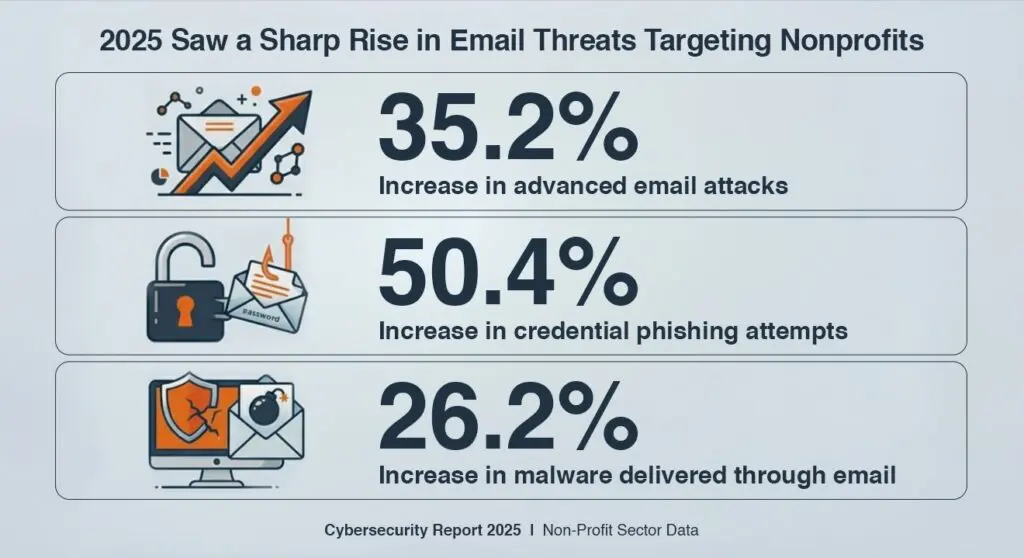
Nonprofits run on trust. Donors expect their contributions to be handled responsibly, beneficiaries rely on their data being protected, and partners depend on consistent operations. That trust is fragile, and cybersecurity now plays a direct role in maintaining it. While most leaders recognize cyber risk, many are not prepared to respond. About 70% of NGOs are unsure whether they could recover from a disruptive cyberattack, turning risk into real operational impact.
Moreover, Nonprofits are managing more data across more systems, often with limited internal resources. Distributed teams, volunteers, and third-party access increase exposure, making it harder to control who has access and how securely they operate. Attackers recognize this gap and target organizations where valuable data exists, but defenses are inconsistent. Cybersecurity is no longer just an IT concern. It is a leadership priority tied to continuity, funding, and long-term stability.
Understanding risk in a nonprofit context requires looking beyond technical vulnerabilities and focusing on how attacks affect operations, funding, and reputation.
Phishing remains the most common entry point. About 83% of organizations experienced a phishing attack in the last year. Nonprofits are particularly exposed because communication with donors, sponsors, and vendors is frequent and often time-sensitive. A well-crafted email that appears to come from a donor or board member can lead to credential theft or unauthorized financial transfers.
Ransomware poses a direct threat to service delivery. For nonprofits, system downtime is not just an inconvenience. It can halt programs, delay services, and disrupt communities that rely on them. Losing access to donor databases or case management systems for even a few days can have a measurable impact on funding and outcomes.
Data exposure carries both ethical and legal consequences. Nonprofits often handle sensitive personal information, including financial records and data related to vulnerable populations. A breach does not just create compliance issues. It directly impacts the people the organization is trying to support.
Limited internal resources increase risk. Many nonprofits lack dedicated cybersecurity leadership or structured security programs. A study by NTEN found that only about 40% of nonprofits provide regular cybersecurity training. This creates gaps that attackers can exploit through social engineering and credential-based attacks.
Reputation damage has long-term effects. Donor trust is difficult to rebuild once lost. A single incident can reduce future donations, delay grants, and impact partnerships. Cybersecurity incidents are no longer contained events. They influence how stakeholders evaluate the organization moving forward.
Consider a simple but damaging scenario. An attacker gains access to your website or donation platform and alters the banking details associated with online contributions. Donors continue giving, unaware that funds are being redirected. In other cases, a compromised donation page can be used to collect card details, exposing donors to fraud while the organization loses both revenue and trust. This is where cybersecurity for nonprofits becomes critical, as even small gaps can lead to significant financial and reputational damage.
Cybercriminals know nonprofits are mission-driven and use that urgency to their advantage. They research organizations, map users and systems, and spend days or weeks finding the easiest way in. In many cases, they quietly gain access, move through email and cloud accounts, and wait for the right moment to act.
Nonprofits offer a strong return for that effort. Donor records, payment details, healthcare data, and personal information can be sold or used for fraud. Timing and access make these attacks effective. When teams are moving quickly, a single convincing message or small system change can lead to financial loss.
For nonprofit leaders, the most important question is not how an attack happens, but what it means for the organization when it does.
A successful attack can lead to:
These are not isolated IT issues. They affect fundraising, service delivery, and overall organizational stability. Cybersecurity decisions should be evaluated with the same level of importance as financial planning and program strategy.
Strong cybersecurity does not start with tools. It starts with structure, accountability, and consistency. The following controls form the foundation of a resilient nonprofit security program.
A cybersecurity policy sets expectations across the organization. It defines how staff should handle data, devices, passwords, and email. It also establishes accountability and provides a reference point for decision making.
This policy should not be static. It needs to be reviewed regularly, communicated clearly, and reinforced through training. As the organization grows and adopts new technologies, the policy should evolve to reflect those changes.
Nonprofits need clear visibility into what data they collect, where it is stored, and who has access to it. Donor information, financial records, and personal data should only be accessible to authorized individuals.
Data governance also includes understanding legal and regulatory requirements. Whether it involves donor privacy laws or healthcare data regulations, leadership must ensure that data handling practices align with compliance expectations.
Technology alone does not prevent breaches. People play a critical role in identifying and stopping threats. Regular training helps staff recognize phishing attempts, suspicious activity, and risky behaviour.
Given that only about 40% of nonprofits provide ongoing training, this is one of the most immediate opportunities to reduce risk. Training should be practical, relevant, and continuous rather than a one-time initiative.
Multi factor authentication is one of the most effective ways to prevent unauthorized access. It blocks more than 99.9% of automated account compromise attempts.
MFA should be required for email, cloud platforms, and any system that provides access to sensitive data. This is a low-cost control with a high impact on reducing risk.
Backups are essential for recovery. In the event of ransomware or system failure, they provide a way to restore operations without paying a ransom.
Backups should be encrypted, immutable, tested regularly, and stored separately from the primary network. Leadership should also ensure that recovery processes are documented and tested to avoid delays during an actual incident.
Beyond core controls, nonprofit leaders should focus on building a structured approach to managing cyber risk. This involves aligning security initiatives with operational priorities and ensuring that decisions are made with a clear understanding of risk and impact.
A risk assessment provides visibility into current vulnerabilities and potential threats. It helps prioritize investments and ensures that resources are allocated effectively. This should be conducted regularly and updated as the organization changes.
Weak or reused passwords remain a common entry point for attackers. Enforcing strong password requirements and encouraging the use of password managers can significantly reduce this risk.
Cybersecurity is not just an operational issue. It is a governance issue. Board members should understand the risks, the organization’s current posture, and the potential impact of an incident. This ensures that cybersecurity is included in strategic discussions and funding decisions.
Sensitive information should not be shared through unsecured channels. Implementing secure communication tools and guidelines helps protect data in transit and reduces the risk of interception.
Outdated systems create vulnerabilities that attackers can exploit. Regular patching and updates ensure that known security issues are addressed promptly. This should be managed through a structured process rather than ad hoc updates.
An incident response plan defines how the organization will respond to a cyber event. It should include roles, responsibilities, communication protocols, and recovery steps.
This plan should be tested through exercises to ensure that teams are prepared. During an incident, speed and clarity are critical. A well-defined plan reduces confusion and helps contain the impact.
Many nonprofits approach cybersecurity reactively. Controls are implemented after an incident or when a requirement arises. This approach creates gaps and leaves the organization exposed.
Leadership teams need to shift toward a proactive model where cybersecurity is integrated into planning, budgeting, and operations. This includes:
Cybersecurity is not about eliminating all risk. It is about managing risk in a way that protects the organization’s ability to operate, serve, and grow.
Nonprofits exist to create impact. Cybersecurity supports that mission by ensuring that operations remain stable, data remains protected, and trust remains intact.
The organizations that will succeed in the coming years are those that treat cybersecurity as a leadership priority rather than a technical afterthought. This often includes working with experienced partners that deliver Managed IT Services for Nonprofits, helping bring structure, visibility, and accountability to cybersecurity efforts.
For nonprofit leaders, the question is not whether to invest in cybersecurity. It is whether the organization is prepared to operate without it.
To connect, please enter the 6-digit code given to you by your Network Administrator: