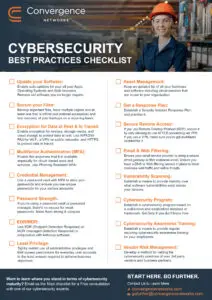
Cybersecurity Best Practices Checklist for Manufacturing
Use this checklist to identify security gaps across your environment and understand where your organization stands.
Download the Guide
What This Checklist Helps You Do
This guide is designed to help manufacturing leaders:
- Identify gaps across IT and operational systems
- Assess whether core security controls are implemented
- Validate remote access and access management policies
- Evaluate backup, recovery, and response readiness
- Strengthen governance and vendor risk oversight
It provides a structured way to review your current posture without requiring technical expertise.
Built for Real Manufacturing Environments
Manufacturers face unique risks, including plant-floor connectivity, remote vendor access, legacy systems, and supply-chain dependencies.
This checklist is tailored to manufacturing organizations that need to:
- Protect uptime and production continuity
- Reduce exposure to ransomware and credential attacks
- Improve visibility into vulnerabilities
- Align security practices with recognized frameworks
- Prepare for audits, insurance reviews, or compliance requirements
Contact Us
Get Started

















